Security Sage's Guide to Hardening the Network Infrastructure: Andres, Steven, Kenyon, Brian, Pack Birkholz, Erik: 9781931836012: Amazon.com: Books

Cisco NEXUS IOS Hardening Guidelines v2.0.docx - Cisco Nexus Hardening Guidelines Allied Bank ITG-Network Headoffice | Course Hero
PPT - Cisco Router/Switch Hardening Colorado Springs Cisco Users Group April 8, 2003 PowerPoint Presentation - ID:4356547
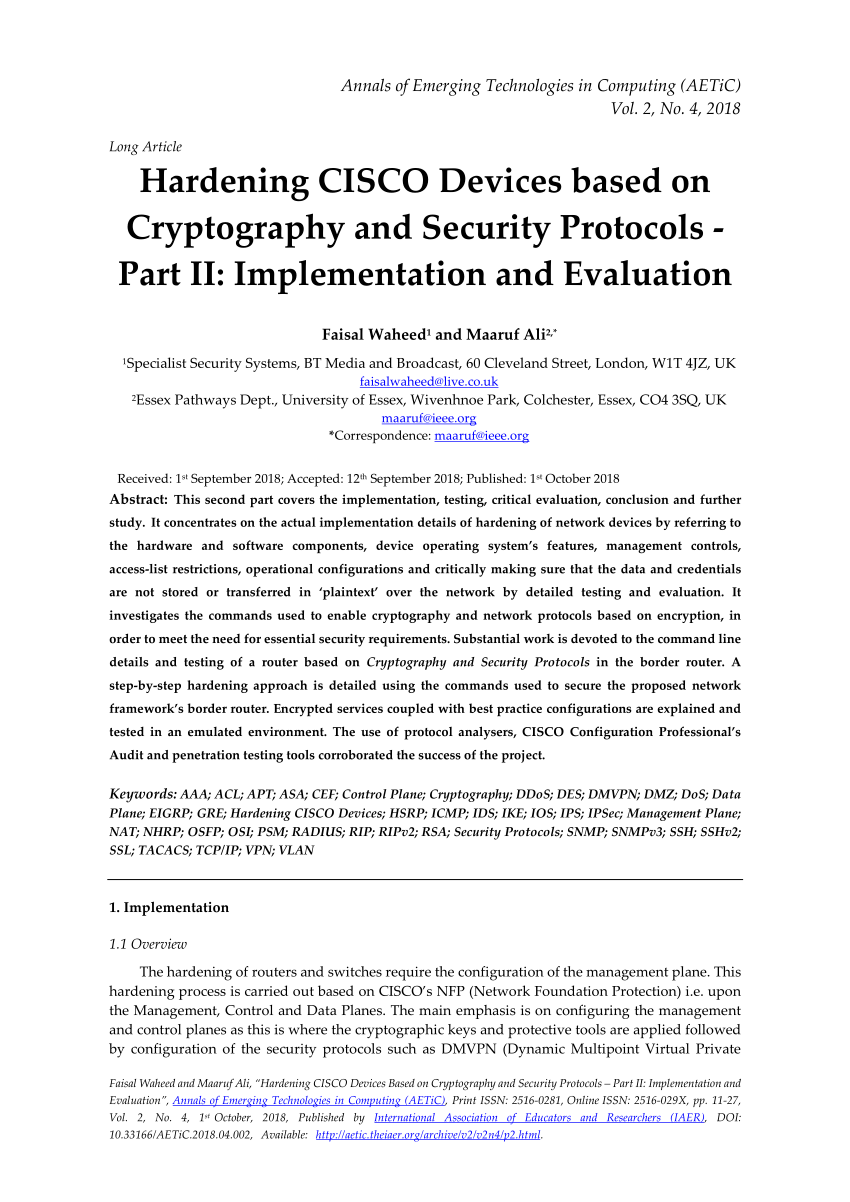
PDF) Hardening CISCO Devices based on Cryptography and Security Protocols - Part II: Implementation and Evaluation